Staff at a government laboratory have revealed they’ve been using a quantum internet since late 2010. But it’s an extremely simple model and might not scale well.
The idea of a quantum internet scales from quantum computing, which used the magnetic orientation of atomic particles as a way to encode 0s and 1s. Simply put, atomic particles are pretty darn small, even compared with silicon chips, which makes for extremely powerful processors. The atomic system also allows for parallel computing (carrying out multiple tasks simultaneously) on a single processor, without the need to use multi-cores.
However, connecting two quantum computers together over a network becomes trickier. The nature of quantum physics where observation changes a state means that in principle you can’t relay data: the moment an intermediary machine tries to “open” the data, it changes its state and effectively destroys the message.
The good news is that this makes communication much more secure as there’s no way to read or copy information mid-transmission. The bad news it that this largely limits you to direct connections.
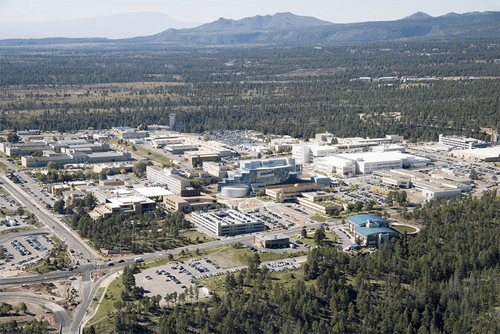
Researchers at the Los Alamos National Labs (pictured) say they’ve been running a quantum internet using a spoke and hub model. This means messages go through a central hub where they are read (destroying the original data) and then converted back into quantum bits using a newly generated encryption key and sent securely to their destination. That allows any two machines to communicate securely even though they aren’t directly connected.
The system has a couple of major limitations. The hub must be kept completely secure (electronically and physically) otherwise every communication is compromised. The system also relies on the hub being online and working at all times.
Another problem is that it’s difficult if not impossible for a computer sending a message to get confirmation that it’s been received at its intended destination.